Posted inDatabase
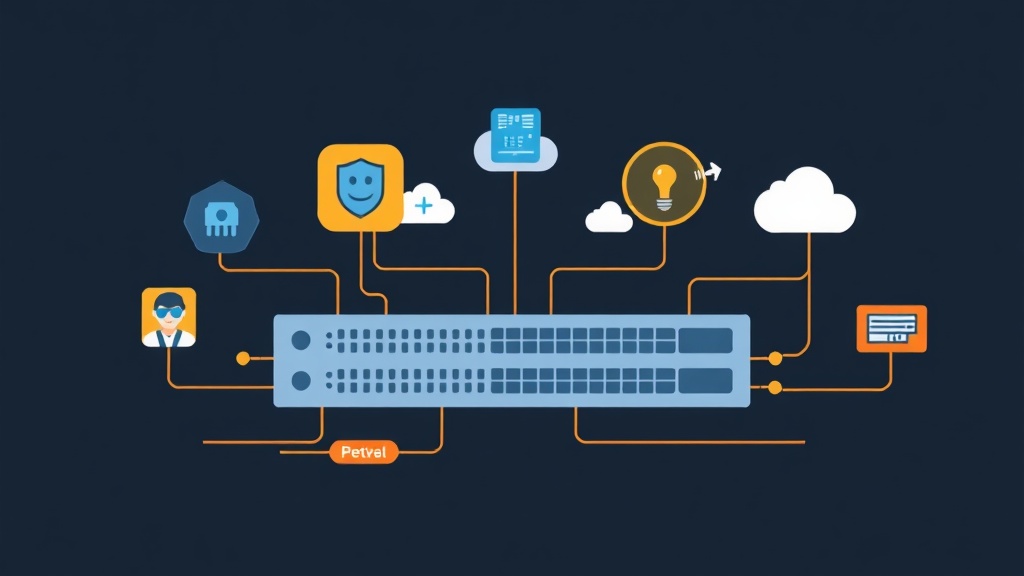
Mastering Database Branching with Neon: No More 2 AM Production Disasters
Tired of production migrations failing due to 'data gaps'? Discover how Neon's database branching lets you test against real production data in isolated, instant environments.