Posted inHomeLab
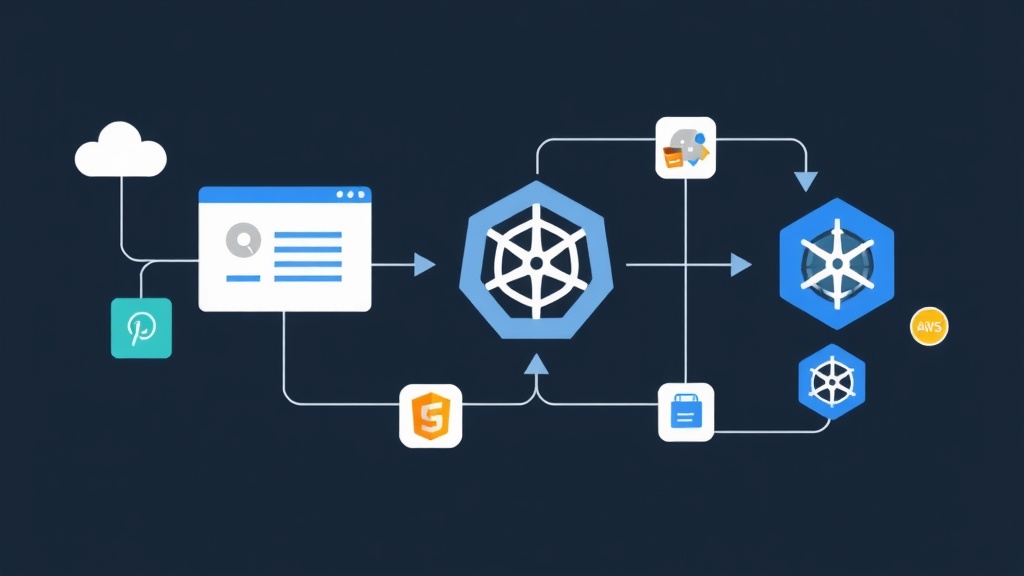
Ditch the Password Sticky Notes: Deploying Authentik SSO in Your HomeLab
Tired of re-typing passwords for 15 different apps? Learn how to deploy Authentik to centralize your HomeLab security with SSO and Multi-Factor Authentication.