Picture this: It’s 2 AM. Your phone rings. It’s an alert: ‘Web Server 1 DOWN.’ You scramble out of bed, heart pounding, trying to figure out why your application is suddenly inaccessible. That single point of failure just bit you, hard. Your users are seeing errors, and you’re in full firefighting mode. Sound familiar?
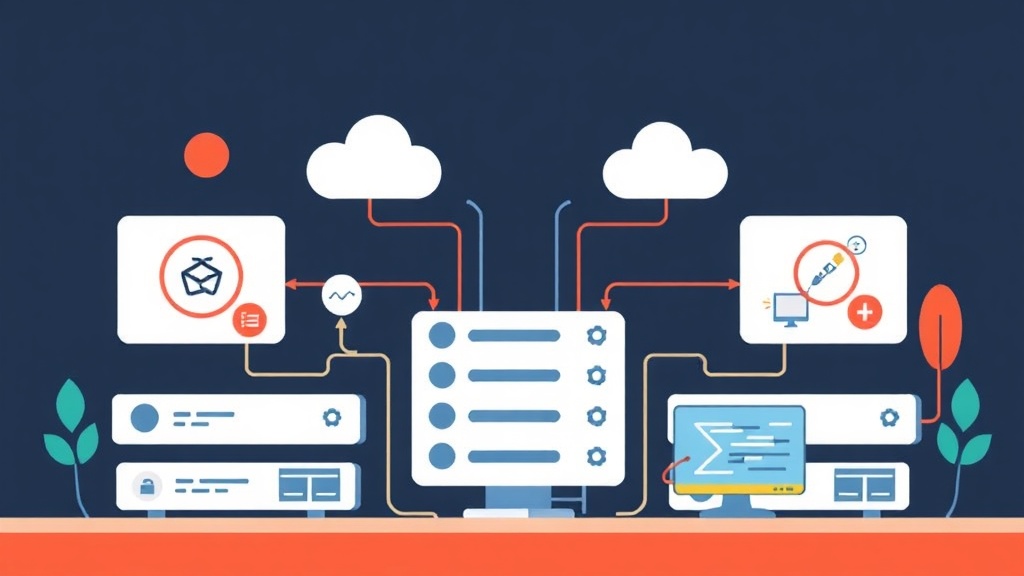
Load balancers are your first line of defense against downtime, ensuring your application stays online even when a backend server unexpectedly fails. They do more than just distribute traffic. Today, I’ll walk you through setting up High Availability (HA) for your web applications using two robust tools: HAProxy and Nginx.
Quick Start (5 min): Get a Basic HAProxy Load Balancer Running
When an incident strikes, a quick fix is paramount. Here’s how to get a basic HAProxy setup running rapidly, distributing traffic across two backend web servers. For this example, assume you have two web servers (like Nginx or Apache) already running on 192.168.1.101:80 and 192.168.1.102:80, and your HAProxy server is located at 192.168.1.100.
Step 1: Install HAProxy
On your load balancer server (192.168.1.100):
sudo apt update
sudo apt install haproxy -y
For RHEL/CentOS systems, you would use sudo yum install haproxy -y or sudo dnf install haproxy -y.
Step 2: Configure HAProxy
Open the HAProxy configuration file: sudo nano /etc/haproxy/haproxy.cfg
Delete or comment out its existing content and add this minimal configuration:
frontend web_frontend
bind *:80
mode http
default_backend web_servers
backend web_servers
mode http
balance roundrobin
server web1 192.168.1.101:80 check
server web2 192.168.1.102:80 check
A quick breakdown:
frontend web_frontend: This section defines the entry point for incoming requests.bind *:80: HAProxy listens for connections on all available network interfaces on port 80.mode http: HAProxy operates at Layer 7 (the HTTP layer), allowing for advanced HTTP-specific routing.default_backend web_servers: All traffic received by this frontend is directed to theweb_serversbackend pool.backend web_servers: This defines the group of actual web servers that will handle client requests.balance roundrobin: Traffic is distributed sequentially, sending requests one by one to each server in the backend pool.server web1 ... check: This line defines a specific backend server and enables continuous health checks to monitor its availability.
Step 3: Enable and Start HAProxy
sudo systemctl enable haproxy
sudo systemctl start haproxy
sudo systemctl status haproxy
Step 4: Test Your Setup
Open your web browser and navigate to the HAProxy server’s IP address (e.g., http://192.168.1.100). You should see content from one of your backend web servers. Refresh your browser a few times, and you should observe responses from the other server.
To truly test high availability, try stopping one of your backend web servers—for example, by running sudo systemctl stop nginx on 192.168.1.101. HAProxy will promptly detect the failure and cease sending traffic to it, ensuring your application remains online. Trust me, debugging this under pressure at 2 AM is an experience you want to avoid.
Deep Dive: Understanding Load Balancing Fundamentals and HAProxy
While that quick setup can be a lifesaver, it’s essential to understand the underlying mechanics and how to construct a more robust system.
What is Load Balancing?
A load balancer distributes incoming network traffic across multiple backend servers. This isn’t just about optimizing speed; it’s crucial for:
- High Availability (HA): If one server fails, the load balancer routes traffic to the healthy ones, preventing downtime.
- Scalability: As your user base grows, you can add more backend servers without reconfiguring clients.
- Performance: Distributing requests prevents any single server from becoming a bottleneck.
HAProxy Basics: The Workhorse of Reliability
HAProxy (High Availability Proxy) is a free, open-source solution renowned for delivering high-performance and reliable load balancing and reverse proxy capabilities for TCP and HTTP-based applications. It’s often my preferred choice for dedicated load balancing tasks.
Key Configuration Sections:
global: This section defines system-wide parameters, such as logging settings, user/group permissions, and the maximum number of connections.defaults: These settings apply by default to alllisten,frontend, andbackendsections unless explicitly overridden.frontend: This block defines the public-facing listener—the IP address and port where HAProxy accepts incoming client connections.backend: This section defines the group of actual servers that the frontend will forward client requests to.listen: A convenient combination of afrontendandbackendblock, often used for simpler, self-contained configurations.
Load Balancing Algorithms:
roundrobin: Distributes requests sequentially to each server in the pool. It’s a simple, widely used, and effective method.leastconn: Directs new connections to the server currently handling the fewest active connections. This algorithm is particularly effective for applications with long-lived connections.source: This method hashes the client’s source IP address to ensure that the same client consistently connects to the same backend server. It’s useful for maintaining session persistence without relying on cookies.uri/url_param/hdr: These are more advanced methods that distribute requests based on specific components of the HTTP request, such as the URI, a URL parameter, or an HTTP header.
Health Checks: The Heartbeat of HA
The check keyword, which we used in our earlier example, instructs HAProxy to periodically probe the backend servers for their operational status. You can fine-tune this behavior with additional parameters:
inter <delay>ms: The interval between health checks (e.g.,inter 2000mschecks every 2 seconds).rise <count>: The number of consecutive successful checks required for a server to be considered ‘up’ and rejoin the pool.fall <count>: The number of consecutive failed checks after which a server is marked as ‘down’ and removed from the active pool.
Detailed HAProxy Configuration Example
Let’s expand our previous configuration to include more common production-grade settings, like a stats page and SSL termination (or passthrough).
global
log /dev/log local0
chroot /var/lib/haproxy
stats socket /run/haproxy/admin.sock mode 660 level admin expose-fd listeners
stats timeout 30s
user haproxy
group haproxy
daemon
maxconn 20000 # A high value, suitable for busy load balancers. Adjust based on expected traffic.
defaults
log global
mode http
option httplog
option dontlognull
timeout connect 5000ms
timeout client 50000ms
timeout server 50000ms
errorfile 400 /etc/haproxy/errors/400.http
errorfile 403 /etc/haproxy/errors/403.http
errorfile 408 /etc/haproxy/errors/408.http
errorfile 500 /etc/haproxy/errors/500.http
errorfile 502 /etc/haproxy/errors/502.http
errorfile 503 /etc/haproxy/errors/503.http
errorfile 504 /etc/haproxy/errors/504.http
frontend http_in
bind *:80
mode http
# Uncomment the line below to redirect HTTP to HTTPS, forcing SSL for all traffic.
# redirect scheme https code 301 if !{ ssl_fc }
default_backend web_servers
frontend https_in
bind *:443 ssl crt /etc/ssl/certs/yourdomain.pem
mode http
option httplog
default_backend web_servers
backend web_servers
mode http
balance leastconn
option httpchk GET /healthz
cookie SERVERID insert indirect nocache
server web1 192.168.1.101:80 check cookie web1_id inter 2s rise 2 fall 3 weight 100
server web2 192.168.1.102:80 check cookie web2_id inter 2s rise 2 fall 3 weight 100
server web3 192.168.1.103:80 check cookie web3_id inter 2s rise 2 fall 3 weight 50 backup
listen stats
bind *:8080
mode http
stats enable
stats uri /haproxy?stats
stats realm Haproxy\ Statistics
stats auth admin:password
stats refresh 5s
Observe the option httpchk GET /healthz directive. This tells HAProxy to perform an HTTP GET request to the /healthz endpoint on each backend server to determine its health, offering a more robust check than a simple TCP connect. This method is far more reliable for web applications.
Additionally, the cookie SERVERID insert indirect nocache line enables session persistence, a concept I’ll elaborate on in the tips section. The weight 100 (or weight 50 for web3) parameter controls the relative proportion of traffic a server receives; a higher weight means more requests. I’ve personally implemented this approach in production environments, and the results have consistently demonstrated stability, even under heavy load, preventing numerous potential outages.
Remember to replace /etc/ssl/certs/yourdomain.pem with your actual SSL certificate chain and choose a strong password for the stats page.
Advanced Usage: Nginx as a Load Balancer
While HAProxy is a purpose-built load balancer, Nginx—primarily recognized as a powerful web server and reverse proxy—also provides robust load balancing capabilities. If Nginx is already part of your technology stack, consolidating these roles can often simplify your infrastructure.
Why Nginx for Load Balancing?
- Consolidation: If Nginx already serves static files or acts as a reverse proxy, integrating load balancing into its existing configuration is often straightforward.
- Simplicity (for HTTP/HTTPS): For basic HTTP/HTTPS load balancing, Nginx’s configuration syntax can feel more intuitive, especially for those already familiar with its web server capabilities.
- Rich HTTP Features: Beyond load balancing, Nginx provides a suite of advanced HTTP features, including caching, compression, and URL rewriting.
Nginx Load Balancing Concepts:
upstreamblock: This block defines a logical group of backend servers to which Nginx will distribute requests.proxy_pass: This directive directs incoming requests from aserverblock to a specifiedupstreamgroup.- Nginx Load Balancing Methods:
round-robin(default): Distributes incoming requests evenly and sequentially among the servers in theupstreamgroup.least_conn: Directs requests to the server with the fewest active connections, ideal for long-lived client connections.ip_hash: This method uses a hash of the client’s IP address to determine which server receives the request, ensuring that a specific client consistently connects to the same backend server for session persistence.hash key: Distributes requests based on a custom key you define, such as a URI, a specific header, or a combination of variables.random: Distributes requests randomly across the backend servers.- Health Checks: The open-source version of Nginx includes basic, passive health checks defined by
fail_timeoutandmax_failsparameters. For more advanced, active health checks, you would either need Nginx Plus (the commercial offering) or integration with external monitoring tools.
Nginx Load Balancer Configuration Example
Let’s configure Nginx on 192.168.1.100 to load balance traffic to our two backend web servers.
Step 1: Install Nginx
sudo apt update
sudo apt install nginx -y
Step 2: Configure Nginx
Open the Nginx configuration file: sudo nano /etc/nginx/nginx.conf or create a new file in /etc/nginx/conf.d/loadbalancer.conf.
http {
upstream web_backend {
# default is round-robin
server 192.168.1.101:80 weight=5; # 'weight' determines the proportion of requests this server receives.
server 192.168.1.102:80 weight=5;
# You can add more servers, e.g., 'server 192.168.1.103:80 weight=1 backup;'
# Example of least_conn: uncomment the line below to use it
# least_conn;
# Example of ip_hash for session persistence: uncomment the line below
# ip_hash;
}
server {
listen 80;
server_name yourdomain.com 192.168.1.100;
location / {
proxy_pass http://web_backend;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
# Optional: HTTPS Load Balancing
server {
listen 443 ssl;
server_name yourdomain.com 192.168.1.100;
ssl_certificate /etc/nginx/ssl/yourdomain.crt;
ssl_certificate_key /etc/nginx/ssl/yourdomain.key;
location / {
proxy_pass http://web_backend;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
}
Remember to create the SSL directory and place your certificates there if you’re using HTTPS, and adjust yourdomain.com and IP addresses accordingly.
Step 3: Test and Enable Nginx
sudo nginx -t # Test configuration syntax
sudo systemctl enable nginx
sudo systemctl restart nginx
sudo systemctl status nginx
With this configuration, Nginx will now function as a load balancer. The fail_timeout and max_fails parameters, which you can append to each server line within the upstream block, enable basic passive health checks. For instance, server 192.168.1.101:80 max_fails=3 fail_timeout=30s; signifies that if three requests to 192.168.1.101:80 fail within a 30-second window, Nginx will mark that server as temporarily unavailable for the next 30 seconds.
Practical Tips and Best Practices
While setting up a load balancer is an excellent first step, truly ensuring high availability and seamless operations requires considering these practical tips:
1. Monitor Everything
Don’t just configure your load balancer and forget about it. Continuous monitoring of both the load balancer and all backend servers is crucial. HAProxy’s built-in stats page (as configured in the listen stats block earlier) provides invaluable real-time insights into server status, active connections, and traffic patterns. For Nginx, you’ll typically rely on external monitoring tools that scrape logs or leverage the Nginx stub status module for basic metrics.
2. Session Persistence (Sticky Sessions)
Certain applications require a user to consistently connect to the same backend server throughout their session—for instance, if session data is stored locally on that specific server. This behavior is known as session persistence, or ‘sticky sessions’.
- HAProxy: Use the
cookiedirective in thebackendsection (as shown in the detailed config:cookie SERVERID insert indirect nocache). - Nginx: Use the
ip_hashload balancing method in yourupstreamblock. Be aware that if a user’s IP changes (e.g., mobile network), they might get a new server.
Implement sticky sessions only when absolutely necessary, as they can impede optimal load distribution and reduce the effectiveness of your load balancer.
3. SSL/TLS Termination Strategy
Deciding where to handle SSL/TLS encryption and decryption is a key architectural choice.
- At the Load Balancer: In this model, the load balancer decrypts incoming SSL/TLS traffic and then forwards either unencrypted or re-encrypted traffic to the backend servers. This approach offloads CPU-intensive cryptographic operations from your web servers, allowing them to focus on serving application content. (HAProxy example:
bind *:443 ssl crt /etc/ssl/certs/yourdomain.pem) - At the Backend Servers: Alternatively, the load balancer can simply pass encrypted traffic directly to the backend servers, which then handle the decryption themselves. While this simplifies the load balancer’s configuration, it places a greater processing load on your backend application servers. (HAProxy example:
mode tcpandbind *:443withoutssl crt, thenserver web1 192.168.1.101:443 check).
Generally, terminating SSL at the load balancer is preferred for improved performance and streamlined certificate management.
4. Redundancy for the Load Balancer Itself
What happens if your load balancer itself fails? It instantly becomes a new single point of failure. For genuine high availability, deploying at least two load balancers is essential.
Technologies like VRRP (Virtual Router Redundancy Protocol) combined with keepalived can establish a floating IP address that automatically switches between an active and a standby load balancer. This setup is a crucial next step for any production environment, and I can attest that skipping these redundancy tests will inevitably lead to problems later on. I learned this the hard way during a planned maintenance window that unexpectedly went sideways.
5. Thorough Testing
Before deploying to a production environment, rigorously test your load balancer setup. Simulate various failure scenarios:
- Stop a backend server and verify traffic is redirected.
- Bring the failed server back online and ensure it rejoins the pool.
- Increase simulated load to see how your chosen algorithm performs.
- Test edge cases like network partitions.
Implementing a load balancer marks a fundamental step toward building resilient and scalable web applications. Whether you opt for HAProxy’s dedicated power or Nginx’s versatility, a solid understanding of these concepts will undoubtedly save you from those dreaded 2 AM outage calls and keep your services running smoothly.