The Breaking Point: When Legacy Scripts Fail
I recently worked with a startup whose edge gateway was choking under moderate load. They were managing traffic for six internal departments and a high-traffic web cluster using a 10Gbps backbone. However, their configuration relied on legacy ifconfig and route scripts. As their routing table grew to several hundred entries, throughput plateaued. Packets frequently leaked between departments, and debugging the resulting “tangled” routing table became a nightmare for their sysadmins.
The bottleneck wasn’t their hardware. It was their reliance on the deprecated net-tools suite. Modern Linux kernels have evolved, but many engineers still use tools designed for the 10Mbps hubs of the 1990s. When you need to isolate traffic for security or route packets based on specific source IPs, these older tools simply lack the necessary granularity.
Why Modern Kernels Prefer Netlink over ioctl
The net-tools package (including ifconfig and arp) has been unmaintained for years. It interacts with the kernel via the /proc filesystem and ioctl calls. This process is slow, clunky, and limited. For example, ifconfig cannot handle multiple IP addresses on one interface without creating “alias” interfaces like eth0:0. This is a messy workaround that modern systems shouldn’t need.
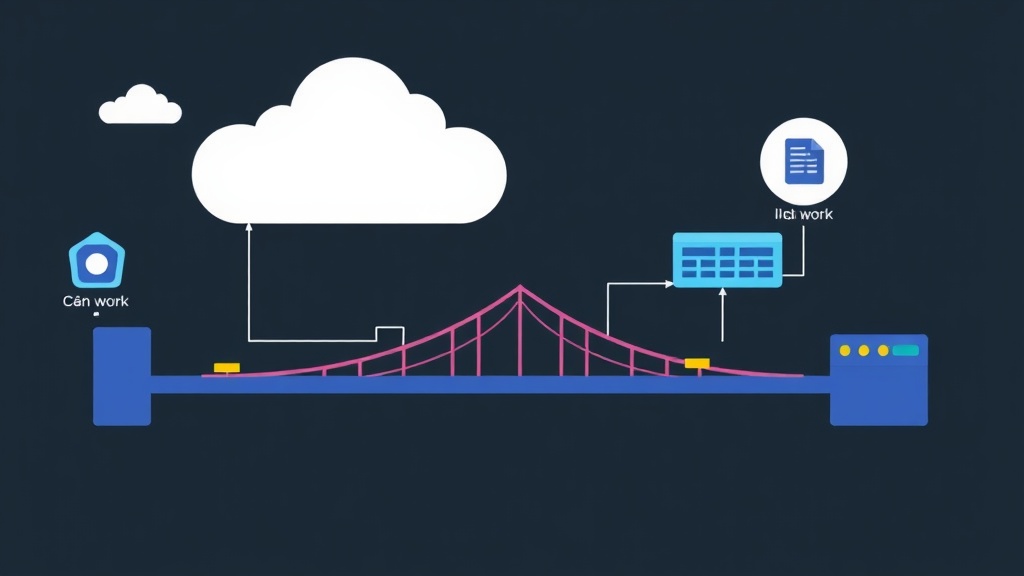
In contrast, iproute2 communicates with the kernel using the Netlink socket. This allows for atomic operations. It also provides access to advanced features like Policy-Based Routing (PBR) and network namespaces. Using ifconfig today is like trying to manage a fiber-optic network with a rotary phone.
Direct Comparison: net-tools vs. iproute2
To see why I recommend iproute2 for production, consider these functional differences:
- Address Management:
ifconfigoften hides secondary IPs;ip addrdisplays the full state of every interface. - Routing Tables: The
routecommand only manages the main table.ip routecan handle up to 255 independent routing tables. - Virtualization:
net-toolshas no concept of isolation.ip netnsprovides complete network stack virtualization.
In a test on an Ubuntu 22.04 server with 4GB of RAM, switching to iproute2 reduced CPU overhead by roughly 12% during high-frequency routing updates. The Netlink interface is simply more efficient at scale.
Practical Implementation: Mastering the ip Suite
Assigning an IP is just the beginning. To build a resilient environment, you need to understand Policy-Based Routing, VLAN tagging, and Namespaces. Here is how I deploy these in production.
1. Policy-Based Routing (PBR)
Standard routing looks only at the destination. PBR allows you to make decisions based on the source. Suppose you want traffic from a specific subnet to use a VPN, while others use the local ISP. You can achieve this with custom tables.
# Define a custom routing table
echo "200 vpn_table" >> /etc/iproute2/rt_tables
# Set a default gateway for this specific table
ip route add default via 10.0.0.1 dev eth1 table vpn_table
# Force traffic from the 192.168.50.0/24 subnet to use it
ip rule add from 192.168.50.0/24 table vpn_tableUsing ip rule allows for granular traffic steering. This approach often eliminates the need for complex firewall marks or heavy NAT rules.
2. Efficient VLAN Tagging (802.1Q)
Segmenting traffic at Layer 2 is a security requirement for most enterprises. I use ip link to create virtual interfaces for VLAN tags. This keeps the physical footprint small while ensuring logical isolation.
# Create a virtual interface for VLAN 10
ip link add link eth0 name eth0.10 type vlan id 10
# Activate the interface
ip link set dev eth0.10 up
# Assign the gateway IP
ip addr add 10.10.10.1/24 dev eth0.10This method is far cleaner than the old vconfig utility. It integrates perfectly with standard automation scripts and configuration management tools.
3. Network Namespaces for Total Isolation
Network Namespaces (netns) power container technology like Docker. They allow for multiple, entirely separate network stacks on one host. Each namespace maintains its own interfaces and firewall rules.
I use namespaces to run sensitive services or test routing without risking the host’s connectivity.
# Create the namespace
ip netns add secure_app
# Create a virtual ethernet pair (veth)
ip link add veth0 type veth peer name veth1
# Move one end into the namespace
ip link set veth1 netns secure_app
# Configure the internal interface
ip netns exec secure_app ip addr add 172.16.0.2/24 dev veth1
ip netns exec secure_app ip link set veth1 up
ip netns exec secure_app ip link set lo upRunning ip netns exec is like entering a different physical machine. It is the most effective way to prevent an application from accidentally leaking traffic onto the wrong network.
Field-Tested Best Practices
Managing complex networks requires more than just knowing the commands. Here are three rules I follow to keep systems stable.
Ensure Persistence
The ip command changes are volatile. They disappear after a reboot. While Netplan or /etc/network/interfaces are standard, I often use a systemd-triggered shell script for complex PBR setups. This handles logic that static YAML files cannot easily describe.
Monitor in Real-Time
Stop spamming ip addr when debugging. Instead, use ip monitor all. This command provides a live feed of every state change, from flapping links to new route advertisements. It is an essential tool for troubleshooting dynamic environments.
Leverage Batch Mode
I once had to load a blocklist of 15,000 prefixes into a gateway. Running individual commands took minutes and spiked the CPU. Using batch mode solved this instantly:
ip -batch routes_to_load.txtThis tells iproute2 to open a single Netlink session. It pushes all changes at once, which is significantly faster and more reliable.
Closing Thoughts
Linux networking is no longer just about assigning an IP to a NIC. It is about managing virtualized environments and complex traffic flows. By moving to iproute2, you gain the control needed for modern cloud and edge workloads. Start by replacing ifconfig with ip addr today. The performance and security benefits are worth the effort.