The Dreaded Black Screen: Why the Boot Process Matters
We’ve all stared at that unblinking cursor on a black screen, wondering if our data just vanished. You hit the power button, the fans whirl, but then… nothing. Or maybe a cryptic grub rescue> prompt mocks you. When I first started managing Linux servers, these moments were pure panic. I felt like I was poking a black box with a stick, hoping for a miracle.
Understanding the Linux boot sequence isn’t just for academics; it’s the ultimate troubleshooting superpower. Having managed over 15 production Linux instances for various clients, I’ve learned that 90% of boot failures are predictable once you know the handoff points. Knowing exactly where the hardware hands off to software lets you pinpoint whether you’re dealing with a dead CMOS battery, a corrupted bootloader, or a hung systemd service.
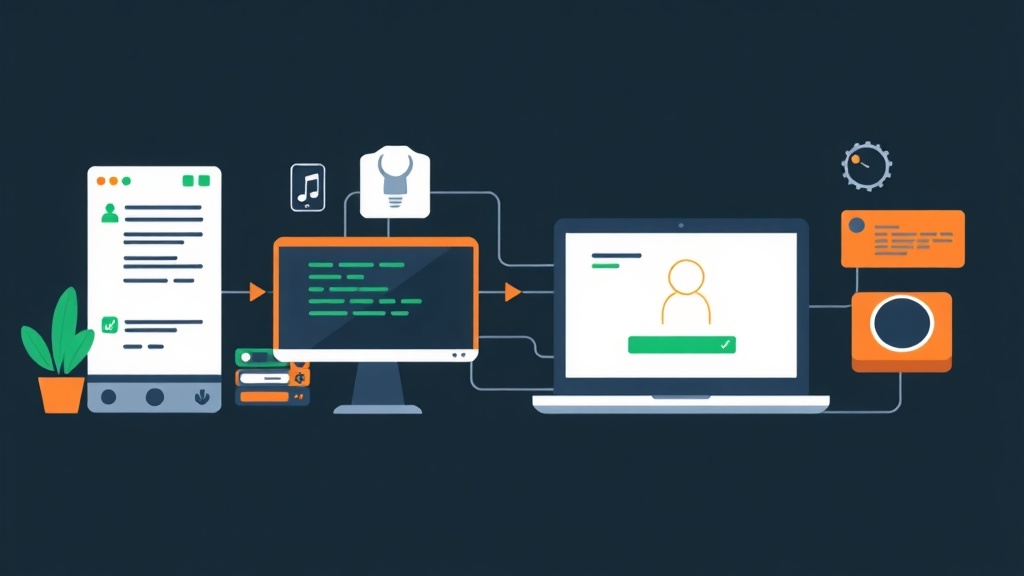
Think of the boot sequence as a high-stakes relay race. Four runners must pass a baton perfectly. If any runner trips, the race stops, and you’re left with a system that won’t start.
The Relay Race: Mapping the Four Stages
You don’t “install” the boot process—it’s baked into your hardware and OS. However, you do need a mental map to navigate it when things go south. The process follows a rigid hierarchy: if Stage 1 fails, Stage 2 never even gets the signal.
Stage 1: Hardware and Firmware (BIOS/UEFI)
The moment electricity hits the motherboard, the firmware takes the wheel. On older hardware (pre-2010), this was BIOS. Modern systems use UEFI (Unified Extensible Firmware Interface), which is essentially a tiny operating system of its own.
- POST (Power-On Self-Test): The firmware runs a quick inventory. It checks if your 32GB of RAM is seated properly and if the CPU is responding. If you hear three short beeps and the screen stays dark, the relay hasn’t even begun.
- Finding the Handoff: BIOS looked for a tiny 512-byte Boot Sector (MBR) at the very start of the disk. UEFI is more sophisticated; it searches for an EFI System Partition (ESP)—usually a FAT32 partition—and executes a specific
.efifile, such as/EFI/ubuntu/grubx64.efi.
Stage 2: The Bootloader (GRUB2)
Firmware is smart, but it doesn’t know how to run Linux. It only knows how to find the Bootloader. Most distros rely on GRUB2. Its primary job is to show you a menu and load the kernel into memory.
Seeing a menu means the firmware succeeded. However, if you’re dumped into a grub> or grub rescue> prompt, it means GRUB found its own code but can’t find its configuration file or the partition containing the kernel.
Stage 3: The Kernel and Initramfs
This is where the actual Linux OS begins its life. GRUB pulls two vital files into RAM: the Kernel (vmlinuz) and the Initramfs (Initial RAM Filesystem).
The kernel is the heart of the system, but it faces a classic catch-22. It needs drivers to read your hard drive (especially for NVMe or encrypted volumes), but those drivers are stored on that very hard drive. The Initramfs solves this. It’s a tiny, temporary root filesystem containing just enough drivers to let the kernel mount the real root partition (/). Once the real disk is mounted, the kernel “pivots” to it and clears the temporary RAM disk.
Stage 4: The Init System (systemd)
Once the real root filesystem is live, the kernel starts the first-ever process: PID 1. On modern distros like Ubuntu, Debian, and RHEL, this is systemd. It’s the grand orchestrator that launches your network stack, SSH server, and finally, the login prompt.
Configuration: How to Intervene
Effective debugging requires knowing how to step into this relay race. The GRUB menu is your primary intervention point.
Editing GRUB on the Fly
If your system hangs during boot, you can often bypass the issue by tweaking kernel parameters. When the GRUB menu appears, hit e to edit. Find the line starting with linux:
linux /boot/vmlinuz-6.5.0-generic root=UUID=a1b2c3d4... ro quiet splashTo see exactly what’s failing, delete quiet and splash. This forces the system to scroll text instead of showing a pretty logo. If you’re locked out, adding init=/bin/bash at the end will drop you straight into a root shell before any security services or passwords are even loaded.
Permanent Fixes
Avoid touching /boot/grub/grub.cfg directly—it gets overwritten every time the kernel updates. Instead, edit /etc/default/grub. For instance, to ensure you always see verbose logs, change the default line:
# Edit /etc/default/grub
GRUB_CMDLINE_LINUX_DEFAULT="nosplash debug"
# Apply the changes
sudo update-grub # Ubuntu/Debian
sudo grub2-mkconfig -o /boot/grub2/grub.cfg # RHEL/FedoraSwitching Targets
Systemd uses “targets” instead of the old runlevels. If your GUI is crashing and preventing a login, you can force the system to boot into a text-only mode to save resources or fix drivers:
# Boot to command-line only (saves ~500MB+ RAM)
sudo systemctl set-default multi-user.target
# Return to the standard desktop interface
sudo systemctl set-default graphical.targetVerification: Why is my Boot Slow?
Reaching the login screen is a win, but performance matters. If your server takes 3 minutes to start, you have a bottleneck.
The ‘Blame’ Game
I use systemd-analyze to audit every server I deploy. It gives a high-level summary of the time spent in the kernel versus userspace.
systemd-analyzeTo find the culprit slowing you down, run:
systemd-analyze blameThis lists services by their start time. I once discovered a misconfigured NFS mount that was timing out and adding exactly 90 seconds to every reboot. A quick fix to /etc/fstab brought the boot time down to under 15 seconds.
Diving into Logs
If a hardware device isn’t showing up, dmesg is your best friend. It shows the kernel’s raw buffer. For service failures, journalctl is the standard:
# Show all errors from the current boot session
journalctl -b -p errMastering these stages changed how I approach Linux. Instead of guessing, I now look for where the baton was dropped. No GRUB menu? Check the EFI partition. Kernel panic? Rebuild the initramfs. No login prompt? Check your systemd units. Once you break the process down, the “black box” becomes a logical, solvable sequence.