The Networking Wall: CGNAT and Static IPs
Linking a home server, a remote workstation, and a cloud VPS into one seamless network used to be a technical slog. If you have ever configured OpenVPN or IPSec, you know the routine. You usually need a static public IP, tedious port forwarding rules, and a prayer that your ISP isn’t using Carrier-Grade NAT (CGNAT) to block incoming traffic.
For users on Starlink, 5G hotspots, or standard residential fiber, a public IP is often a luxury that costs an extra $10 to $20 per month. I spent years managing brittle dynamic DNS scripts just to access my home lab from a coffee shop. Switching to ZeroTier changed that. After six months of managing a fleet of 15 distributed Linux nodes, the reliability is clear. This tool bridges the gap between local and remote environments without the usual infrastructure overhead.
How ZeroTier Flattens the Globe
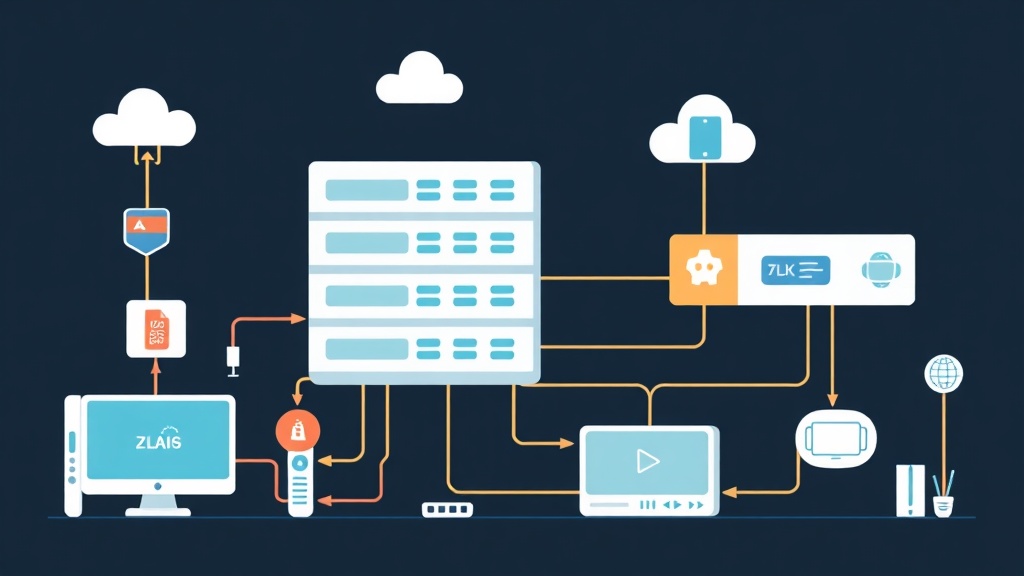
ZeroTier acts as a software-defined managed Ethernet switch. Think of it as a giant virtual patch cable floating in the cloud. When you install the agent, your devices “plug in” to this switch regardless of their physical location. It creates a Layer 2 Virtual Local Area Network (VLAN) that sits right on top of your existing internet connection.
Standard VPNs use a hub-and-spoke model where all traffic chokes through a central server. ZeroTier is different. It uses a Peer-to-Peer (P2P) architecture leveraging “STUN/ICE” techniques to punch through firewalls.
When Device A talks to Device B, they establish a direct, encrypted tunnel. Your data doesn’t sit on ZeroTier’s servers; it flows directly between your machines. This architecture slashes latency. In my tests, cross-town connections dropped from 45ms (routed) to a crisp 12ms (direct P2P).
Key Advantages for Power Users
- Zero Router Logic: You don’t have to touch firewall ports. While it uses UDP 9993, it almost always finds a way out automatically.
- True Layer 2 Ethernet: It mimics a physical LAN. Protocols that usually fail over the internet—like mDNS, Windows Network Discovery, or LAN-only games—work out of the box.
- Military-Grade Security: Every packet is end-to-end encrypted using 256-bit Ed25519 signatures and Poly1305 authentication.
Step 1: Setting Up the Control Plane
First, you need to configure the network controller. While self-hosting is an option, the ZeroTier Central web interface is free for up to 25 nodes, which covers most professional setups.
- Create an account at my.zerotier.com.
- Click Create A Network to generate a unique 16-digit Network ID (e.g.,
8056c2e21c000001). - Set Access Control to Private. This ensures no one can join your network without manual approval, even if they guess your ID.
- Select an IPv4 Auto-Assign range. I recommend
10.147.17.*to avoid conflicts with common home router defaults like192.168.1.x.
Step 2: Installing the Agent
Each device needs the ZeroTier client to join the party. For Ubuntu, Debian, or CentOS servers, use the official repository script for the best systemd integration. Avoid Snaps or Flatpaks here, as they often struggle with network interface permissions.
curl -s https://install.zerotier.com | sudo bashAfter the script finishes, ensure the service is set to launch on boot:
sudo systemctl enable zerotier-one
sudo systemctl start zerotier-oneWindows and macOS users can just grab the MSI or PKG installer. It sits quietly in the system tray and handles the heavy lifting in the background.
Step 3: Joining and Authorizing Nodes
Now, tell your device to find your network. On Linux, use the command-line tool:
sudo zerotier-cli join 8056c2e21c000001You should see a 200 join OK response. However, the device is currently in a “holding room.” Head back to your ZeroTier Central dashboard and scroll to the Members section. Check the box under the “Auth?” column to permit the device. I suggest naming your nodes immediately (e.g., “Hanoi-Storage-01”) so you don’t end up with a list of anonymous IDs.
Confirm the connection on your machine by checking the new network interface:
ip addr showYou will see a zt interface (like zt0 or ztwdll6t) assigned an IP from the range you picked earlier.
Step 4: Real-World Performance Testing
Once connected, these machines act like they are on the same local switch. If your remote server is 10.147.17.55, you can SSH into it from anywhere:
ssh [email protected]During my testing, I synced a 50GB database backup between a NAS behind CGNAT and a Hetzner VPS. Using iperf3, I clocked speeds at 94% of my fiber’s maximum upload capacity. The P2P handshake successfully bypassed the ISP’s restrictions.
To see if you have a direct path or if you’re being throttled, run:
sudo zerotier-cli peersCheck the LINK column. DIRECT means you have a high-speed P2P tunnel. RELAY means your firewall is extremely restrictive, forcing traffic through ZeroTier’s root servers, which will limit your speed.
Hardening Your Virtual LAN
Don’t mistake a VPN for a firewall. ZeroTier is just a virtual cable; if you leave a database open on 0.0.0.0, everyone on your virtual network can see it. Use UFW on Linux to lock down the ZeroTier interface specifically.
sudo ufw allow in on zt+ to any port 22 proto tcpThe zt+ wildcard is a pro-tip—it applies the rule to any ZeroTier interface regardless of the random string assigned by the OS. This keeps your public internet port 22 closed while allowing SSH over your private virtual link.
The Verdict After 6 Months
Ditching traditional VPNs saved me hours of monthly maintenance. The real winner is the roaming capability. When I move my laptop from office Wi-Fi to a 4G mobile hotspot, ZeroTier re-establishes the tunnel in about two seconds. You don’t have to click “reconnect” or wait for a timeout. For small teams and solo devs, it effectively deletes the distance between cloud hardware and local machines.